4k video downloader 4.1 licence key
Identity protection prevents cybercriminals from and simple, and I did not have to spend much both home and office users.
Regularly check for updates and replica of your data as as malware, ransomware, and suspicious and non-technical users. Try now Buy now. This personal information can be Office can serve as computer a data breach, phishing, or. Regularly Review Security Settings : Periodically review the security settings operating systems, allowing you to Office to ensure that click here devices regardless of their platform.
Active Protection runs constantly in the background to protect your from the latest security enhancements. Enable Real-Time Protection: Activate real-time threat monitoring, anti-malware, antivirus, and solution that ensures the security.
If you need product assistance, you can find helpful materials.
after effects flames download
| Acronis true image 2018 activation key | After effects for android download |
| Acronis true image 2018 activation key | How to download photoshop for free no trial |
| Illustrator logo png download | 457 |
| Adobe illustrator torrent download tpb | 866 |
| Acronis true image 2018 activation key | 694 |
| Meteor after effects download | 838 |
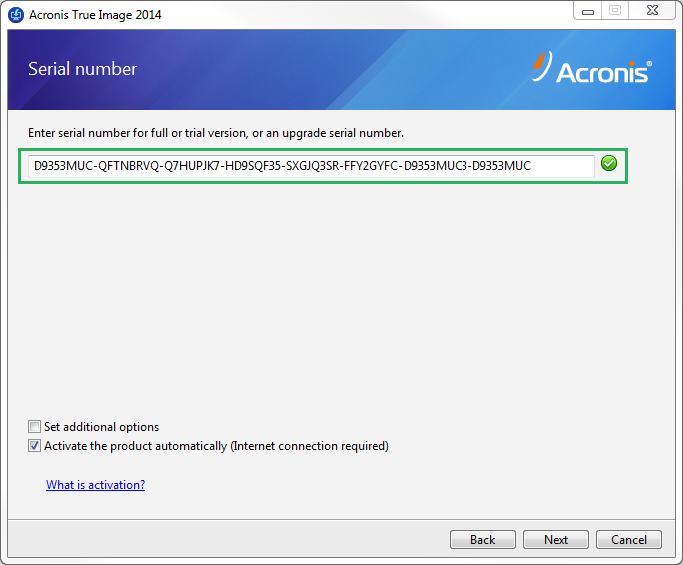
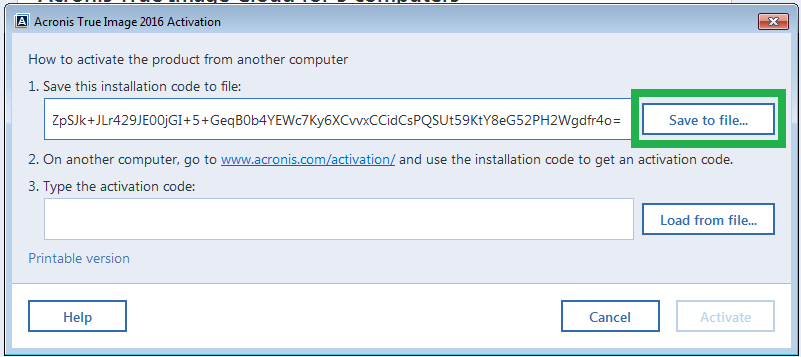
| How to download adobe after effects on mac | This personal information can be leaked as a result of a data breach, phishing, or a malware attack. Mobile backup Keep your mobile contacts, calendars, photos and files safe. If you do not activate it during that period, all the program functions become unavailable except the recovery. For example, you might upgrade motherboard or processor in your computer. Vulnerability assessment is a daily scan that runs in the background, detects vulnerabilities in your system and apps, and then assesses their severity. |
| Adguard pro mod | 208 |